GitLab
Access Token
An analysis of the Internet Archive's data breach via exposed GitLab tokens, com...
The [Internet Archive](https://www.secureblink.com/cyber-security-news/internet-archive-hacked-31-million-users-exposed), a cornerstone of digital preservation, has experienced another significant data breach. This time, the breach occurred through their Zendesk email support platform after threat actors exploited exposed [GitLab](https://www.secureblink.com/cyber-security-news/gitlab-addressed-a-critical-ssrf-flaw-discovered-to-expose-the-orgs'-internal-servers) authentication tokens.
Despite prior warnings, the organization failed to rotate these tokens adequately, leading to unauthorized access to sensitive data.
### Background of the Internet Archive Breach
Beginning last night, numerous individuals reported receiving unexpected emails in response to old [support tickets](https://developer.zendesk.com/api-reference/ticketing/tickets/ticket-attachments/#show-attachment) submitted to the Internet Archive. These emails, originating from the organization's official Zendesk server, alerted users to the breach:
>>> _"It's dispiriting to see that even after being made aware of the breach weeks ago, IA has still not done the due diligence of rotating many of the API keys that were exposed in their gitlab secrets. As demonstrated by this message, this includes a Zendesk token with perms to access 800K+ support tickets sent to info@archive.org since 2018."_
The threat actor emphasized the magnitude of the breach, highlighting access to over 800,000 support tickets submitted since 2018. The authenticity of these emails was verified through email headers that passed all DKIM, DMARC, and SPF authentication checks, confirming they were sent from an authorized Zendesk server.
### Exposure of Personal Identifiable Information (PII)
Compounding the severity of the breach, some users had previously uploaded personal identification documents when requesting the removal of content from the Wayback Machine. Depending on the level of access the threat actor had within Zendesk, these sensitive attachments might now be compromised.
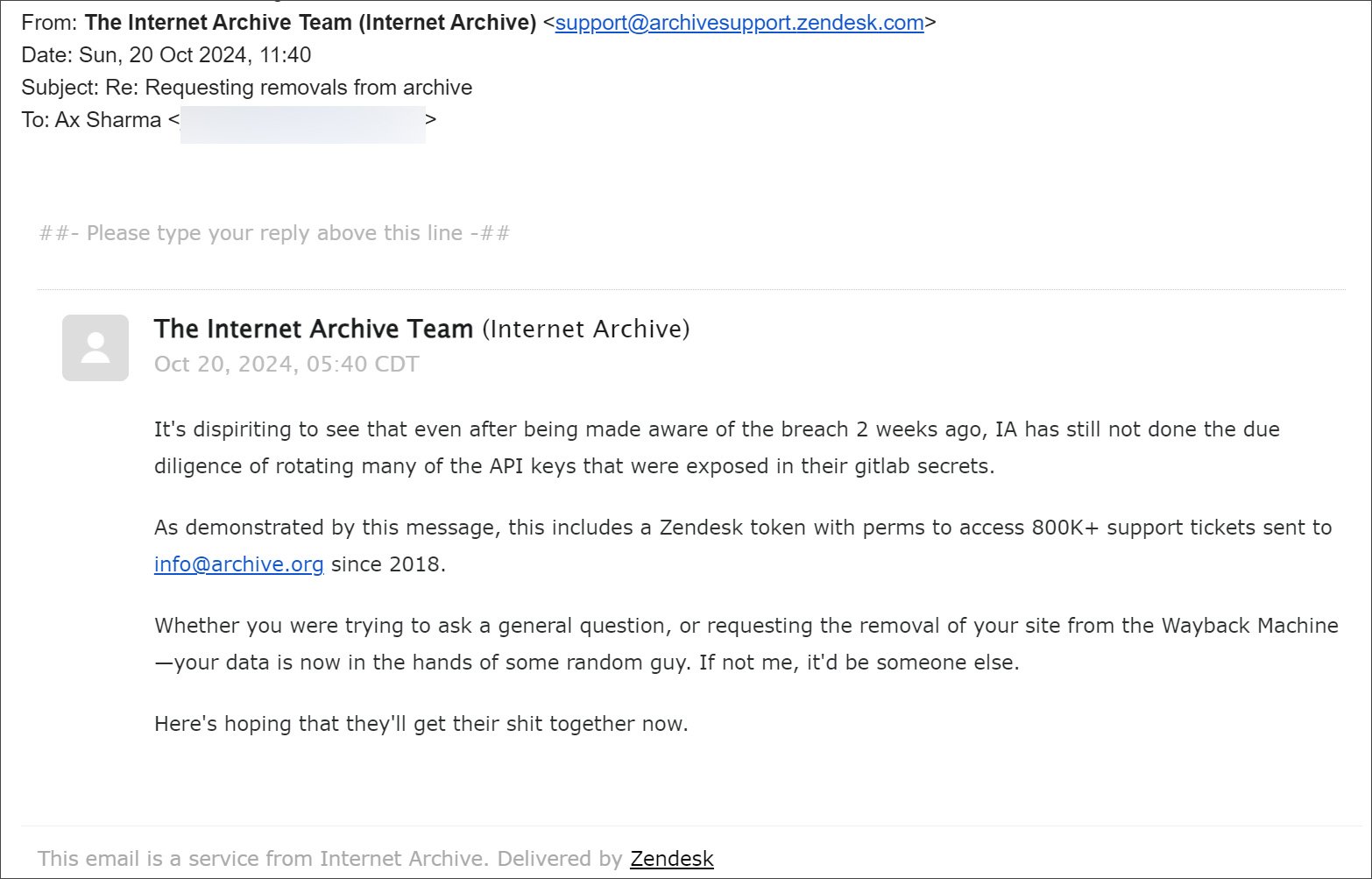
***Email snapshot sent by threat actor to Internet Archive Zendesk (Source: BleepingComputer)***
The Zendesk Attachments API allows users to upload files to support tickets, which are then accessible through links in the agent interface and notification emails.
Attachments are represented as JSON objects containing details like file_name, content_type, and content_url. If the threat actor exploited this API, they could have downloaded personal documents submitted by users.
### Timeline and Failure to Act
BleepingComputer attempted repetatively to [warn](https://www.bleepingcomputer.com/news/security/internet-archive-breached-again-through-stolen-access-tokens/) the Internet Archive about the exposed GitLab authentication tokens. On October 9th, they reported that the Internet Archive suffered two simultaneous attacks:
- 1. A data breach compromising user data for 33 million users.
- 2. A DDoS attack orchestrated by a pro-Palestinian group named SN_BlackMeta.
While these attacks transpired concurrently, they were perpetrated by different threat actors. Misreporting led many to incorrectly attribute the data breach to SN_BlackMeta, frustrating the actual hacker who then reached out to Secure Blink to claim responsibility and provide details.
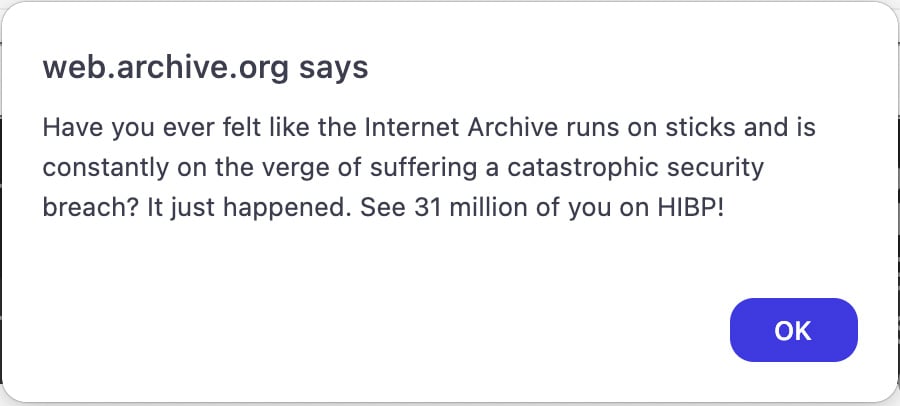
***Data Breach Notification on Internet Archive JavaScript Alert (Source: BleepingComputer)***
### Mechanism of the Breach
The initial point of compromise was an exposed GitLab configuration file on one of the Internet Archive's development servers (services-hls.dev.archive.org).
This file contained an authentication token that had been exposed since at least December 2022. The threat actor used this token to download the Internet Archive's source code.
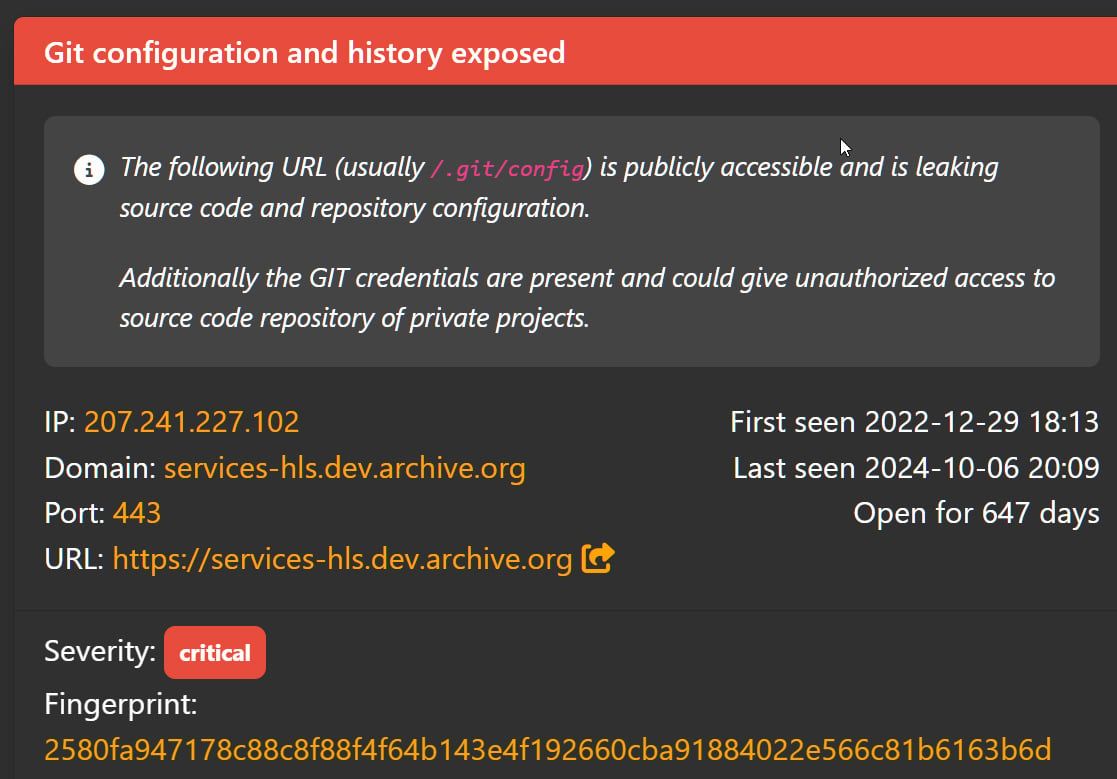
***Internet Archive Exposed GitLab Authentication Token (Source: BleepingComputer)***
Within the source code, additional credentials and authentication tokens were discovered, including those for the organization's database management system. This access allowed the hacker to:
### Download the user database.
#### Access further source code.
**Modify the website.**
The threat actor claims to have exfiltrated 7TB of data, though no samples were provided for verification. The inclusion of API access tokens for the Internet Archive's Zendesk support system in the stolen data further exacerbated the situation.
**Negligence in Security Practices**
Despite multiple warnings from Secure Blink, the Internet Archive failed to rotate the compromised authentication tokens promptly. The threat actor highlighted this negligence in their communication:
>> _"Whether you were trying to ask a general question, or requesting the removal of your site from the Wayback Machine, your data is now in the hands of some random guy. If not me, it'd be someone else."_
This statement attempts to underscores the critical importance of proactive security measures and timely responses to potential threats.
### Understanding the Zendesk Attachments API Vulnerability
The Zendesk Attachments API is designed to facilitate the uploading and attaching of files to support ticket comments. Key functionalities include:
- **Uploading Files:** Users can upload files and attach them to ticket comments.
- **Attachment Accessibility:** Attachments appear as links in the agent interface and notification emails.
- **Attachment Properties:** Attachments are represented as JSON objects with properties such as content_type, content_url, file_name, size, etc.
Given the potential sensitivity of the uploaded files (e.g., personal IDs), unauthorized access to these attachments poses a significant privacy risk. The API documentation specifies that while files are visible to any authenticated user until the upload token is consumed, once associated with a ticket, visibility is restricted. However, in this breach, the threat actor's access to the Zendesk platform could bypass these restrictions.
### Implications for Users and Organizations
The breach has several profound implications:
- **User Data Exposure:** Personal data, including identification documents, may have been compromised.
- **Trust Erosion:** Users may lose confidence in the Internet Archive's ability to safeguard their information.
- **Regulatory Scrutiny:** Potential violations of data protection regulations could lead to legal repercussions.
### Recommendations and Preventative Measures
#### For Users:
- **Monitor Accounts:** Keep an eye on personal accounts for any suspicious activity.
- **Change Passwords:** Update passwords for accounts associated with the Internet Archive.
- **Identity Protection:** Consider credit monitoring services if personal IDs were uploaded.
#### For the Internet Archive and Similar Organizations:
- **Rotate Credentials Regularly:** Implement policies for regular rotation of authentication tokens and API keys.
- **Audit and Monitor:** Conduct frequent security audits to identify and remediate vulnerabilities.
- **Implement Least Privilege Access:** Limit access permissions to only what is necessary for each role.
- **Enhance Incident Response:** Develop robust incident response plans to address breaches swiftly.
The Internet Archive's data breach is not just a stark reminder of the vulnerabilities that can arise from lapses in security protocols. In an era where data is a critical commodity, both organizations and users must remain super weary.
Proactive security measures, timely response to threats, and user education are critical components in safeguarding against such breaches.